Compare to Debian, Ubuntu, RHEL, etc., where you can compile your own newer package, install it
None of these operating systems have Verified Boot. Desktop systems are inherently less secure than mobile devices.
even replace core operating system components
Don't you see the problem there?
and then seamlessly upgrade to the OS vendor’s version when they catch up.
That's not true either. Swapping out random parts of the OS will certainly lead to breakage and dependency hell in your package manager (unless you just replace files without using the package manager, which might make all of this even worse).
and don’t offer any way to install patches, besides building it again
Normal Android behavior. This will be the case for ANY Android-based OS with Verified Boot enabled.
and this is just TPM for Android
This isn't comparable to TPM at all. TPM is a very insecure way of providing a hardware keystore. It can easily be bypassed. Here's a demonstration of that https://www.youtube.com/watch?v=wTl4vEednkQ
I’ve opposed TPM from the start
TPM in desktop machines neither really provides a benefit, nor does it inconvenience the user. I've also opposed to it from a security perspective, since it's misleading and makes users think that it's actually secure and comparable to proper secure elements (such as the Titan M2, Apple Secure Enclave Processor, or the Qualcom SPU), while it really isn't.
I don’t want a device that keeps secrets from me.
It's not keeping secrets from you, the secure keystore is keeping cryptographic secrets away from attackers. Only you can use the cryptographic secrets from the secure element, by combining them with your PIN/passphrase (in a key derivation function) to derive the keys used for full disk encryption. Without a secure element that safely guards these secrets and throttles unlock attempts, attackers like law enforcement agencies can easily brute force your 6 digit PIN and gain full access to your device, including all of your data. The iPhone 11 was the last iPhone generation without a proper secure element. A 6 digit passcode was also bypassed on the iPhone 11 Pro Max, just a few months after its release. https://appleinsider.com/articles/20/01/15/fbi-reportedly-accessed-locked-iphone-11-pro-max-with-graykey-third-party-tool
This hasn't been possible anymore since the iPhone 12, which was released with the Secure Enclave Processor. This is even confirmed by leaked internal documents from forensics companies, such as Cellebrite: https://discuss.grapheneos.org/d/14344-cellebrite-premium-july-2024-documentation
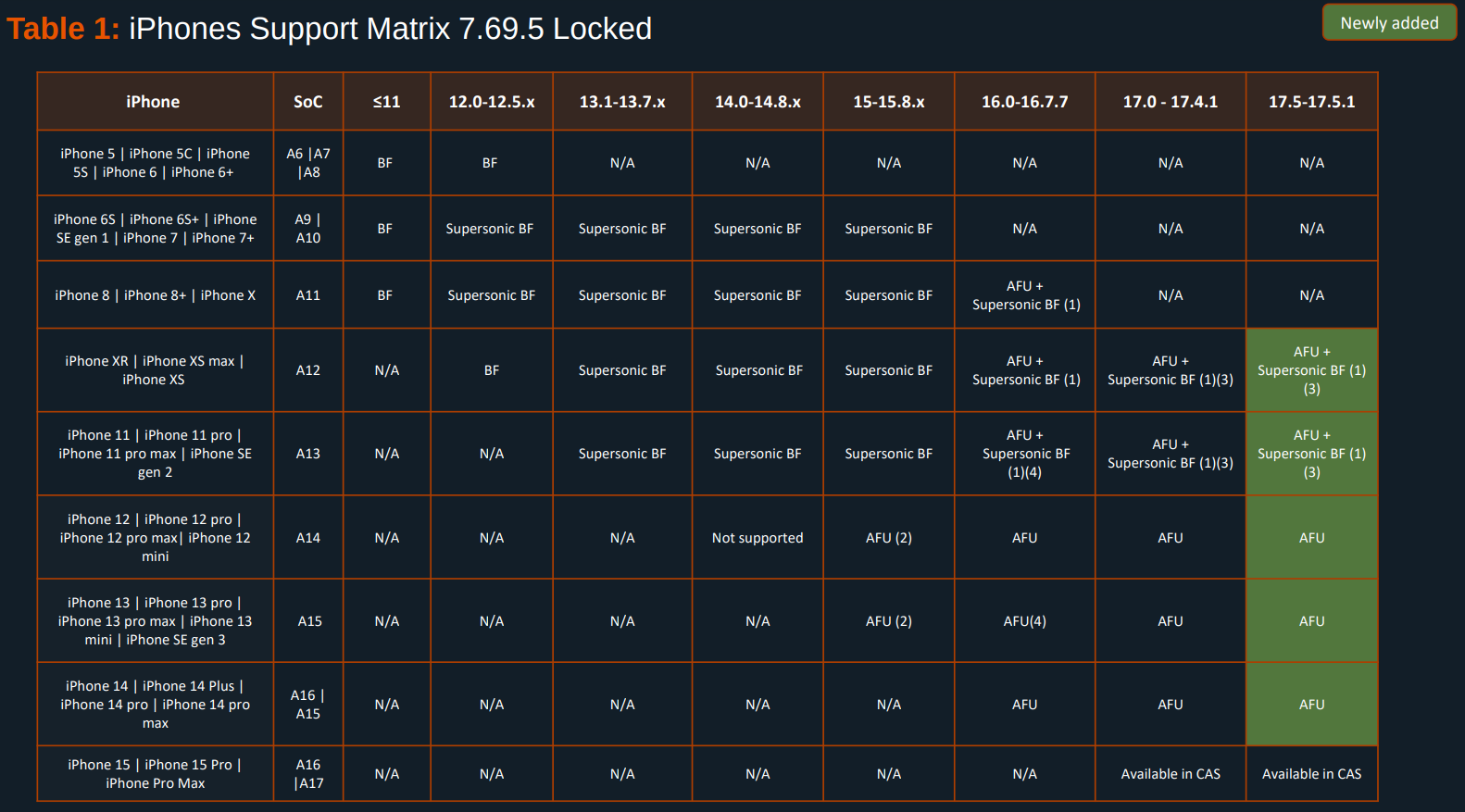
Specifically, I recommend looking at this chart:
It clearly shows that data cannot be extracted from iPhones with secure elements, unless the device is in the AFU state, meaning that the encryption keys are kept in memory.
I do want comprehensive backups, including all cryptographic keys.
Having a secure element to isolate keys there doesn't make sense if you can just export them. The security of those keys cannot be guaranteed anymore, once they're outside of the secure hardware keystore. This is not unique to Android/mobile devices. Look at U2F hardware security tokens, such as the YubiKey or NitroKey. You can't export your keys there either, which is by design, and it's a good thing.
I’m fully aware that Widevine won’t run on a device where the owner has control over the whole device.
This has nothing to do with Widevine. The vast majority of Android devices currently on the market doesn't have a secure element. Widevine still works on these devices.
and you seemingly can’t do it incrementally
What do you mean? Generating an incremental update .zip package and flashing it over your stock GrapheneOS installation? No, that's certainly not gonna work, due to Verified Boot verifying that the signature of the update package matches the signature of the OS that's installed. This is a very important security feature, and prevents attackers (could just be cybercriminals, but that can also include law enforcement, intelligence agencies, etc.) from hacking into update servers and delivering mallicious updates to users. If I remember correctly, that's how EncroChat got bugged by the French police. They hacked into the update servers that were hosted by OVH, and then distributed mallicious update packages, gaining access to the devices of all EncroChat users.
since you have to flash an entire operating system at a time
That is correct. Changing the signing keys requires you to unlock the bootloader, wipe the Verified boot keys, and replace them with a new set of trusted custom (i.e. non-stock) keys. Otherwise someone could just flash a mallicious OS over your current OS, while retaining all of your data. They could then use it to extract your data.
Of course you can easily make changes and install new versions incrementally, once you have installed your custom OS and signing keys to the device. Also, none of this is some crazy GrapheneOS invention, it's the default Android Verified Boot behavior, which GrapheneOS builds upon.